Securing Digital Systems, Applications, and Business Operations
In an increasingly digital world, cybersecurity is essential to protect applications, data, and business operations from evolving threats. Modern systems face risks ranging from misconfigurations and insecure code to advanced cyberattacks that can lead to data breaches, downtime, and loss of trust.
We help organizations build secure-by-design systems by identifying risks early and strengthening security across applications and infrastructure. Our approach combines industry best practices, real-world attack knowledge, and clear, actionable guidance to ensure security is practical, effective, and aligned with business goals.
MES Infrastructure & IT-OT
MES Infrastructure & IT-OT Integration Services
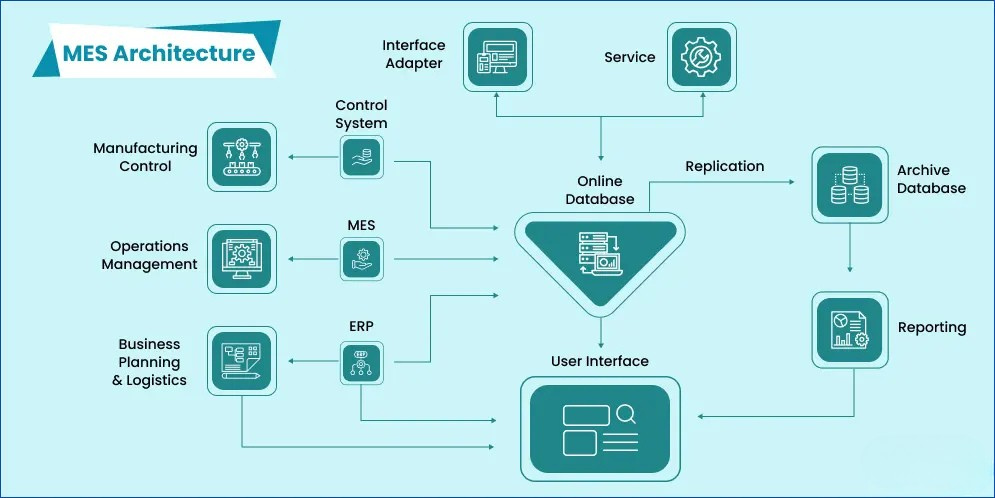
Modern manufacturing and industrial operations require seamless communication between enterprise IT systems and operational technology (OT) environments. Manufacturing Execution Systems (MES) play a critical role in bridging this gap by connecting plant-floor operations with enterprise applications such as ERP, analytics platforms, and cloud systems. However, successful MES deployment requires a secure and well-designed IT-OT infrastructure.
Tapasya Tech provides end-to-end consulting, architecture design, and implementation services for MES infrastructure and secure IT-OT integration, ensuring reliable connectivity, cybersecurity, and scalable industrial network architecture.
IT-OT Environment Assessment
We analyze your current OT network, devices, and IT systems to identify gaps and prepare the infrastructure for MES deployment.
Secure Network Architecture Design
Designing reliable industrial networks with segmented IT-OT zones, industrial switches, firewalls, and secure communication channels.
Industrial Network Infrastructure
Deployment and configuration of industrial Ethernet switches, VLAN segmentation, redundancy planning, and network optimization for factory environments.
Secure MES Connectivity
Integration of MES with PLCs, SCADA, ERP systems, and cloud platforms, ensuring secure and reliable data exchange.
OT Cybersecurity Implementation
Implementation of industrial firewalls, secure remote access, device monitoring, and compliance with standards like IEC-62443 to protect industrial operations.
MES Infrastructure Benchmarking & Standards
OT Cyber Security
Protecting Industrial Systems That Keep Your Business Running
Operational Technology (OT) refers to the systems that control and monitor physical processes in industries such as manufacturing, power generation, utilities, oil & gas, and transportation. These include machines, controllers, sensors, industrial networks, and control rooms.
Unlike office IT systems, OT environments must run continuously. Any downtime, failure, or cyber incident can impact production, safety, and people. Because of this, OT cybersecurity requires specialized knowledge and careful implementation.
We help organizations protect their industrial systems from cyber threats without interrupting operations or affecting safety.



Our OT Cyber Security Services
OT Asset Discovery & Risk Assessment
We identify all OT systems, devices, and networks across your environment to provide complete visibility and uncover security risks, enabling informed decisions and prioritized remediation.
Secure Network Design & Segmentation
We design resilient OT network architectures that isolate critical systems, limit attack propagation, and strengthen operational reliability.
OT-Safe Vulnerability Assessment
We assess security weaknesses using OT-safe techniques that protect system availability and safety while delivering actionable remediation insights.
OT Penetration Testing (Controlled & OT-Safe)
We conduct carefully controlled penetration testing to validate security defences against real-world attack scenarios without impacting industrial operations.
OT Monitoring & Incident Response
We continuously monitor OT environments for suspicious activity and respond swiftly to incidents to minimize operational impact and downtime.
IEC 62443 Compliance Support
We guide organizations through IEC 62443 compliance by assessing gaps, aligning controls, and improving overall industrial cybersecurity maturity.
Why OT Cyber Security Is Important
- Prevents unexpected production shutdowns
- Reduces safety risks to people and equipment
- Protects industrial systems from ransomware and targeted attacks
- Improves visibility and control across OT environments
- Supports regulatory and industry compliance
Product Security
Securing Products Throughout Their Entire Lifecycle
Product security focuses on protecting products that include hardware, software, firmware, and embedded systems. Security issues in products can affect customers directly, lead to recalls, regulatory penalties, and long-term damage to brand reputation.
We help organizations integrate security into product development so products are secure from initial design through deployment and ongoing updates.



Our Product Security Services
Secure Product Design Review
We review product architectures and designs at early stages to identify and mitigate security risks before development and deployment.
Supply Chain Security Review
We assess third-party components, libraries, and vendors to identify and reduce supply chain–related security risks.
Product Security Testing
We test products using real-world attack techniques to uncover vulnerabilities and weaknesses prior to market release.
Security Standards & Compliance
We support alignment with global product security standards to improve security posture and meet regulatory requirements.
Standards Supported:
IEC 62443 • OWASP • NIST
Product Security Outcomes
- Reduced security vulnerabilities in released products
- Faster certification and approval processes
- Increased customer confidence and trust
- Lower cost and effort to fix issues after product release